If your entire SaaS revenue flows through a single payment gateway and that gateway freezes your account, your cash flow drops to zero overnight. It happens more often than you think.
Stripe processes over $1.4 trillion in annual payment volume and powers roughly 80% of the largest U.S. software companies. It is, by most measures, the best payment processor for SaaS. But Stripe can also freeze your funds, hold your payouts, or terminate your account with little warning and less recourse. Monitoring services have documented over 660 Stripe incidents since 2014, averaging more than three per month. Those are just the outages. Account freezes are a different, quieter problem.
Merchants who have had funds frozen describe cycles that are hard to break: payouts stop, customers file chargebacks because refunds cannot be issued, the chargeback rate rises, and Stripe tightens its hold further. Stripe's terms of service authorize reserves on any account at any time, and funds can be held for 180 days or longer after termination. For a SaaS company with monthly recurring revenue as its lifeline, that is not an inconvenience. It is an existential threat.
This post is a guide for SaaS founders and operators who want to build payment redundancy before they need it. We will cover the problem, the architecture, and the services that make it easier. A follow-up technical post will walk through implementation patterns in detail.
The Core Problem: Single Points of Failure in Revenue
The risk is not limited to account freezes. There are three distinct failure modes that a single-gateway dependency creates.
Account termination or fund holds. This is the catastrophic scenario. Your account is flagged, payouts stop, and your operating capital evaporates. It can happen because of a spike in chargebacks, a shift in your business model that triggers a risk review, or simply because your category is reclassified. Businesses that are not traditionally "high-risk" get caught in this. One merchant reported $130,000 frozen after a dispute rate that only rose because Stripe was already holding funds, preventing timely refunds.
Gateway outages. Stripe maintains impressive uptime, but no service is immune. During Black Friday through Cyber Monday 2025, Stripe processed $40 billion while maintaining 99.9999% uptime. That is extraordinary. But 99.9999% of $40 billion still leaves room for failed transactions, and your SaaS renewal cycle does not wait for an all-clear from a status page.
Involuntary churn from failed renewals. When a payment fails and you have no fallback processor, that subscriber churns. Subscription billing platforms report that failed renewals during gateway outages can spike involuntary churn significantly, and recovery is never 100%.
The solution to all three is the same: maintain at least one secondary payment gateway that is active, configured, and warm.
Why "Warm" Matters More Than "Available"
Setting up a Braintree or Adyen account and leaving it dormant does not constitute redundancy. Payment processors monitor transaction patterns. An account that processes zero transactions for six months and then suddenly receives your entire monthly volume will trigger the same risk flags you are trying to avoid. The processor may freeze the new account, hold funds for review, or flag the spike as potential fraud.
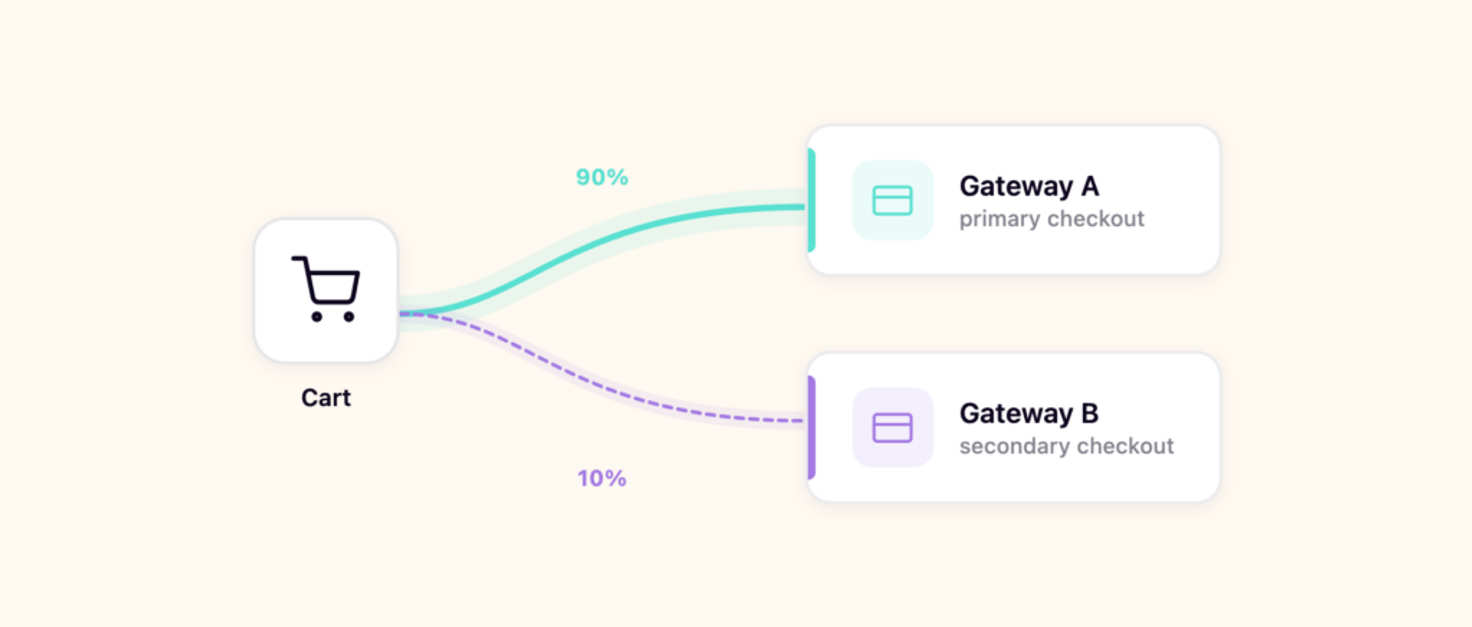
Keeping a secondary gateway "warm" means routing a small, consistent percentage of transactions through it at all times. This establishes a transaction history, builds a relationship with the processor's risk systems, and means your secondary gateway already has active payment methods on file when you need to shift traffic.
The percentage does not need to be large. Five to 10 percent of new subscriptions is enough to maintain a credible transaction pattern. The goal is a steady baseline, not an even split.
Programmatic Methods for Traffic Distribution
There are several approaches to routing transactions across gateways, ranging from simple to sophisticated.
Feature flags with percentage rollouts. This is the most accessible approach for most SaaS teams. Services like LaunchDarkly, Flagsmith, or even open-source tools like Unleash support percentage-based rollouts that deterministically assign users to variations. You create a flag called something like payment-gateway with two variations (primary and secondary) and set the rollout to 90/10. New subscriptions are routed accordingly, and you can shift the percentage in real time without a deploy.
The key advantage is operational simplicity. Your engineering team is likely already using feature flags. Adding a payment routing flag requires no new infrastructure, and percentage changes happen instantly through a dashboard.
Weighted random assignment at the application layer. If you do not use a feature flag service, a simple weighted random function in your payment service achieves the same result. Generate a random number for each new subscription, and if it falls below your threshold, route to the secondary gateway. Store the assignment so renewals continue through the same gateway.
Round-robin or modular assignment. Route every nth transaction to the secondary gateway. This is predictable and easy to audit, but less flexible than percentage-based approaches when you need to shift traffic quickly.
Health-check-based failover. Monitor your primary gateway's API health and automatically route to the secondary when the primary degrades. This handles outages but does not solve the "warm account" problem on its own, since the secondary would still see zero traffic during healthy periods. Combine this with percentage-based routing for the best of both worlds.
Each of these approaches is straightforward to implement. The harder problem is managing payment data across gateways.
Managing Separate Payment Gateways in Your Backend
The architectural challenge is not routing. It is payment method portability. When a customer enters their card on your checkout page, that card is tokenized by whichever gateway processes the transaction. A Stripe token cannot be used with Braintree, and a Braintree token cannot be used with Adyen. If you need to move a customer between gateways, you either need to re-collect their payment information or use a gateway-agnostic token vault.
There are three patterns for managing this.
Pattern one: gateway-specific token storage. Each gateway vaults its own tokens. Your database records which gateway holds each customer's payment method. Renewals always route through the gateway that holds the token. This is the simplest approach, but it means customers assigned to one gateway stay there unless they re-enter payment details.
Pattern two: gateway-agnostic vault. Services like Spreedly or Primer provide a PCI-compliant vault that stores payment methods independently of any gateway. You tokenize once through the vault, and the vault can then transact against any of 120-plus connected gateways. This is the most flexible approach and the one that truly enables gateway portability, but it adds a dependency and a cost.
Pattern three: dual tokenization at checkout. During the initial checkout, tokenize the payment method with both gateways simultaneously. The customer enters their card once, and your checkout flow creates tokens on both Stripe and your secondary processor. This provides immediate portability without a third-party vault, but adds complexity to your checkout implementation and requires both gateways to support your checkout UX.
For most SaaS companies processing under $5 million annually, pattern one is sufficient. Store the gateway assignment per customer, route renewals accordingly, and accept that migrating existing customers between gateways requires them to update their payment method. For companies where gateway migration needs to be seamless, pattern two with an orchestration layer is worth the investment.
Your database schema, at a minimum, needs a payment_gateway field on the customer or subscription record, the gateway-specific token reference, and logic in your billing service that routes to the correct gateway based on that field.
Tactical Approaches by Pricing Model
The right redundancy strategy depends on how you charge.
Flat-rate subscriptions. This is the simplest case. Assign new subscribers to a gateway at signup and renew through that gateway. A 90/10 split keeps your secondary warm. If your primary goes down, shift the split to 0/100 and new signups flow to the secondary immediately. Existing subscribers on the primary will fail and can be retried on the secondary if you have dual tokens, or wait for the primary to recover.
Usage-based or metered billing. More complex because charges are variable and often high-volume. Your secondary gateway needs to handle the same invoice amounts and frequencies. Consider routing a specific customer segment (such as those below a certain usage threshold) to the secondary full-time, rather than splitting randomly. This gives the secondary a predictable, natural transaction pattern.
Tiered pricing with upgrades and downgrades. Mid-cycle proration charges and plan changes add complexity. Ensure your secondary gateway integration handles the same subscription lifecycle events as your primary: upgrades, downgrades, cancellations, refunds, and prorations. Test these flows in your secondary gateway's sandbox regularly.
One-time purchases or credits. If your model includes one-time purchases alongside subscriptions, these are ideal candidates for the secondary gateway. Because they are self-contained transactions with no renewal dependency, they sidestep the token portability problem entirely. No stored payment method needs to persist across gateways. That makes them the lowest-risk traffic for keeping your secondary account active, and a natural starting point if you are not ready to implement a gateway-agnostic vault for your subscription billing.
Services That Make This Easier
Depending on your pricing model and scale, several categories of services can simplify multi-gateway management.
Payment orchestration platforms sit between your application and multiple gateways, providing a single API for routing, failover, and token management. Spreedly connects to over 120 gateways through one integration and includes a portable, PCI-compliant vault with smart routing and automatic failover. Primer offers similar orchestration with a visual workflow builder. These are the most comprehensive solutions, but they add a per-transaction cost and a new dependency.

Subscription billing platforms like Chargebee and Recurly support multiple gateway configurations natively. You can designate a primary and backup gateway, and the platform handles failover and retry logic. If you are already using one of these, multi-gateway support becomes a mere configuration change rather than an engineering project.
Merchant of record services like Paddle and FastSpring take a different approach entirely. As the merchant of record, they handle payment processing, tax compliance, and billing on your behalf. You are insulated from gateway-level risk because the payment relationship is between the MoR and the customer, not between you and Stripe. The trade-off is higher fees (typically 5% plus a per-transaction charge) and less control over the checkout experience.
Feature flag services like LaunchDarkly, Flagsmith, or Unleash handle the traffic routing layer. They do not manage payments directly, but their percentage rollout capabilities are exactly what you need for distributing traffic across gateways.

For a fintech-adjacent SaaS or any product handling sensitive financial data, the regulatory landscape adds another layer. We wrote about navigating fintech regulations for U.S. startups that covers the compliance considerations worth reviewing alongside your payment architecture decisions.
Why Stripe Should Still Be Your Primary
None of this is an argument against Stripe. It is an argument for not depending entirely on any single processor.
Stripe earned its dominance for good reasons. Its API design remains the industry standard for developer experience, supporting 54 programming languages and frameworks with documentation that other processors struggle to match. Roughly 78% of SaaS and subscription businesses use Stripe, and 80% of the Forbes Cloud 100 build on it. The ecosystem of products around it, including Billing, Radar, Connect, Tax, and Atlas, means that Stripe is not just a payment gateway. It is financial infrastructure. During Black Friday and Cyber Monday 2025, Stripe processed $40 billion while maintaining 99.9999% uptime. That is the kind of reliability you want as your primary.
But reliability at the platform level does not protect you from account-level risk. A risk review, a chargeback spike, or a policy change can freeze your specific account regardless of Stripe's overall uptime. And when your SaaS revenue comes primarily from one source, that account-level risk is a business-level risk.
The answer is not to avoid Stripe. It is to use Stripe as your primary while maintaining a warm secondary that can absorb traffic if something goes wrong. Think of it the way you think about backups: the best time to set one up is before you need it.
What Comes Next
This post covered the why and the what. A follow-up technical post will cover the how: implementation patterns for multi-gateway routing in software built on technologies like Django and React, with database schema design for gateway-agnostic billing, webhook handling across processors, and testing strategies for failover scenarios.
The broader landscape of fintech software and infrastructure continues to evolve rapidly, and payment redundancy is becoming table stakes for SaaS companies that take operational resilience seriously.
If you are building a SaaS product and want to ensure your payment infrastructure is resilient from the start, or if you are dealing with the consequences of a single-gateway dependency right now, we would like to hear from you. We build financial software for companies that cannot afford downtime, and payment architecture is one of the problems we solve.


